UAC stands for “User Account Control”. This is a field of software management that isolates the operating system’s core components from potentially damaging changes. This is the level of access that in Unix-like systems is called “root” and in Windows systems is known as Administrator privileges.
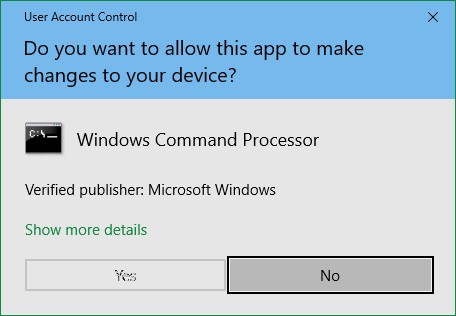
The most frequent encounter that users of Windows get with UAC occurs when they try to install a new piece of software. That popup message asking for authorization in order to permit the installation is the public face of UAC.
More about UAC
User Account Control has been integrated into Windows since Windows Vista in 2006 and it has been included in Windows Server since version 2008.
The UAC system lets user-installed software run in the user area of the drive and only software installed by the Administrator account gets access to system resources. Software that has been installed by the Administrator can be run by users without access to system resources or run by the Administrator to get that system access.
The purpose of UAC is to strengthen system security. It is assumed that the Administrator in a secure business environment is only accessible by an IT professional who will only install authorized, verified software. Users, on the other hand, can’t always be trusted to take precautions about what they download.
Users can easily be tricked into downloading malware that is embedded in an image or a PDF file. Without the Administrator privilege, software that gets access to the endpoint through a user account, will not be able to get into important services.
Areas of the disk that are blocked to user accounts include the %ProgramFiles%, %Windir%, %Windir%\system32 directories. The UAC service also blocks write access to the HKEY_LOCAL_MACHINE\Software\ registry path.
The UAC popup
That permission popup is a key part of UAC. It triggers a setting in the operating system to either facilitate actions in the OS’s sensitive directories with permission or block that access if permission is refused.
System access should only be necessary during the installation and update of the software. Operating variables, temporary storage, and session data should all be stored in user-owned folders. System settings should only be written to a shared, editable folder, such as %programdata%.
The rigid organization of data and settings is beneficial to all users. If one user on a device is able to customize the software, those personal preferences do not impact the other users on that computer.
Virtualization
There are a number of types of virtualization. The general purpose of this strategy is to use the software in order to create an environment that mimics a real resource, such as a separate server or a PC’s hardware.
One of the most widely implemented types of virtualization is a “virtual machine,” or VM. This is a separate operating system that floats on top of the real OS. It gives the services that a piece of software needs from the operating system without letting that software get real, direct access to the actual OS.
The VM mediates between the software and the operating system. In some instances, this configuration can enable software written for one operating system to run on a computer that doesn’t actually have that operating system installed. For example, it is possible to run software that is written for Linux on a computer that has the Windows operating system. If a virtual environment is available to interpret the Linux- compatible demands of the software into requests the Windows can understand – it is like an interpreter.
UAC virtualization
In the case of a UAC virtualization, the VM operates Windows and runs on top of Windows. The purpose of the double operating system isn’t to provide compatibility in OS but to cater to validated legacy software that genuinely needs access to those system areas when run by users.
Rather than mediating between two different operating systems, the UAC virtualization provides the services that the software needs to run in a user account without breaking the strict system isolation of UAC. Access to the folders that the software needs is blocked and that fact would cause the program to hang or fall over.
The implementation of UAC virtualization was a necessary step in order to bridge the introduction of User Access Control. Without this stop-gap measure, much of the software built to run on Windows would cease to function. Although software houses would, in time come to write new versions of their products, the complete rewrite that UAC required would have taken time. Such major changes are usually reserved for new editions and are not accounted for as updates.
Software houses that specialized in products for Windows could not afford to write off the investment already made in their products. When new editions are produced, the vendors calculate a service life for them and wait until all costs have been recovered before writing new versions.
The UAC virtualization maps between the system folder demands of legacy software and the user-owned folders that Windows now expects software to use when run from user accounts.
Thanks to the UAC virtualization, software that writes to C:\Program Files\<Application Path>, is really writing to %LOCALAPPDATA%\VirtualStore\<Application Path>. Thus, a mapping interface between folders in the virtualization keeps old software working while protecting reserved system directories.
The Application Manifest
Not all software is going to need access to protected system areas. Some programs download as executable files and run from wherever they are resident on the computer. The main issue of whether or not a program needs to write files to reserved directories comes down to a matter of the organization of folder access needs.
The installer signals to the operating system what folder access the program expects both for installation and whenever it is run through entries in the Application Manifest. This is an XML document that accompanies the programs in an installer package.
A permission level requirement value within the file is the key to whether Windows will invoke UAC virtualization for this program whenever it is run. Possible values for requestedExecutionLevel are:
- asInvoker Run with the same access token as the parent process.
- highestAvailable Acquire the highest privileges the current user can obtain.
- requireAdministrator This program can only run as Administrator.
Windows will always use UAC virtualization for software that is flagged with the requireAdministrator access need. This type of software will always provoke the appearance of the UAC permission popup whenever it is run. This status is the default. So, if there is no application manifest, or the required execution permission statement is missing, the software will automatically have the requireAdministrator status and will always be virtualized.
When UAC virtualization is invoked
UAC virtualization is a mechanism within Windows, it can’t be applied at will. There is no UAC hypervisor package in circulation. It isn’t a utility in a developer framework and there isn’t an API for it. In short, you can’t command the use of UAC virtualization.
The UAC virtualization process doesn’t apply to all software. Here are some circumstances to keep in mind over whether UAC virtualization will be used for an application:
- UAC Virtualization is only invoked for software when it is run from a user account. Applications running as Administrators don’t need it.
- UAC Virtualization has to be enabled and active on the host.
- Programs running in a 64-bit environment don’t need UAC virtualization. It only applies to 32-bit software.
- The user account needs to have write access to the files in the original file path.
Managing User Account Control
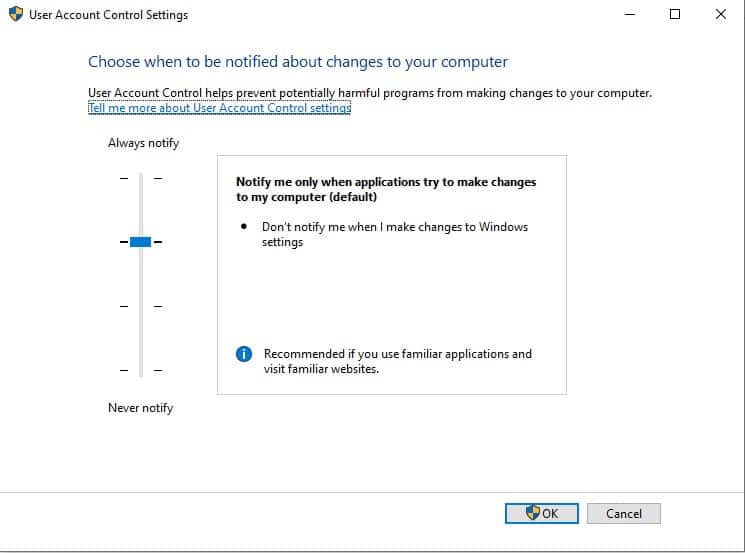
The User Account Control behavior can be modified on each computer that runs Windows. This option is available in the Settings menu and you can get to it by clicking on the Settings cog icon in the Start menu and then typing User Account Control into the Settings search bar.
The User Account Control settings screen is presented as a slider. This gives the user the option of switching between one of four settings for UAC. These options are:
- Always notify
- Notify me only when programs try to make changes to my computer
- Notify me only when programs try to make changes to my computer (do not dim my desktop)
- Never notify
Below, you will find a little more detail about each of these options.
Always notify
This is the most rigid setting. It invokes the notification popup when a program is about to be installed or updated and when you, or any programs, try to change Windows settings. It will freeze all tasks on the computer until you respond.
This option is recommended for computers where new software is frequently installed and for people who visit unfamiliar websites.
Notify me only when programs try to make changes to my computer
This is the default value for UAC. It will notify the computer’s user when programs try to install software or make changes to your computer. It won’t put up the permission popup when you make changes to your computer’s settings yourself. It will freeze all tasks on the computer until you respond.
This option is recommended for those who frequently install new software and visit unfamiliar websites, but don’t want to be notified over their own actions that alter Windows settings.
Notify me only when programs try to make changes to my computer (do not dim my desktop)
This option provokes the permissions popup when programs try to install software or make changes to the computer but it won’t notify those users who make changes to Windows settings manually. Unlike the previous two options, this setting will not freeze other tasks or wait for a response.
This option is only recommended if, for some reason, the notification process works slowly on the computer to the point where it becomes a serious inconvenience to the user.
Never notify
This option disables User Access Control. You will not get the permissions popup under any circumstances.
This option creates a security risk.
Registry Virtualization
Registry virtualization is the application of UAC virtualization to the system registry. The purpose of this feature is to block access to global registry entries while enabling software that requires such access to continue to function. As UAC interprets folder access and diverts write actions to user-controlled directories, Registry virtualization switches attempts to write to global variables to safer user account registry keys.
As with file-based UAC virtualization, the software proceeds with all of its pre-written procedures, creating and updating registry key values without harming those global registry areas.
Registry virtualization is only implemented in order to enable legacy systems to continue operating. The need for this service is probably, by now, almost completely defunct. Any software that was written after 2006 will not need the registry virtualization service because it should have been written along with Microsoft developer guidelines. These guidelines explain the difference between global registry entry use and the registry keys that are available to user accounts.
The future of UAC virtualization
UAC virtualization was created to ensure backward compatibility when Microsoft launched its new architecture. It is a method for preventing legacy software from failing because they are no longer permitted to write to the files whose paths and names are hardcoded.
This shows that UAC virtualization has no future – it is all about the past. The UAC virtualization system has become progressively more redundant as time passes. As UAC has been part of Windows since 2006, it has been an environmental certainty for 25 years. The chances of software written more than 25 years ago still being active without any new versions or updates are slim. For one thing, old software is very prone to attack by hackers. Vulnerability scanners particularly look for old software when probing computers and networks for a way in.
UAC virtualization in Windows 10
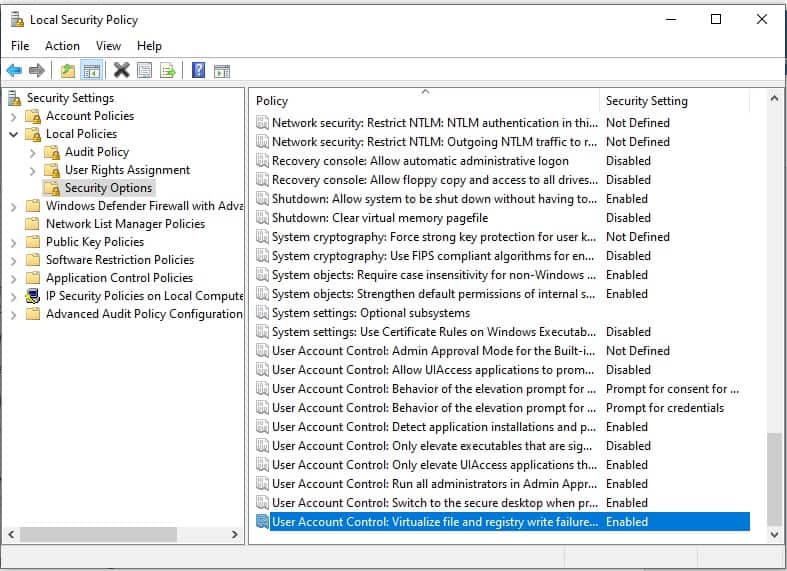
If you are running Windows 10 you might decide to search for your UAC virtualization setting and see whether the function is turned on.
In order to do this:
- Press the Windows button plus “R” to open a Run box.
- Type secpol.msc and press “OK” to open the Local Security Policy app.
- In the Local Security Policy window, expand Local Policies and click on Security Options in the left panel.
- Scroll down the list of policies in the main panel until you get to User Account Control: Virtualize file and registry write failures to per-user locations.
The status of this setting should be Enabled. If it isn’t:
- Double-click on the User Account Control line. A popup will appear.
- Click on the Enabled radio button.
- Click OK to close the popup.
Other system protection methods
A typical Windows user shouldn’t need to worry about UAC virtualization and a designer of software that is intended for use on Windows also need not be concerned with UAC virtualization because current Windows programming practices make this service unnecessary.
There is a comprehensive Windows Security system that protects devices from tampering and there are a few settings that you can look at within Windows in order to improve system protection.
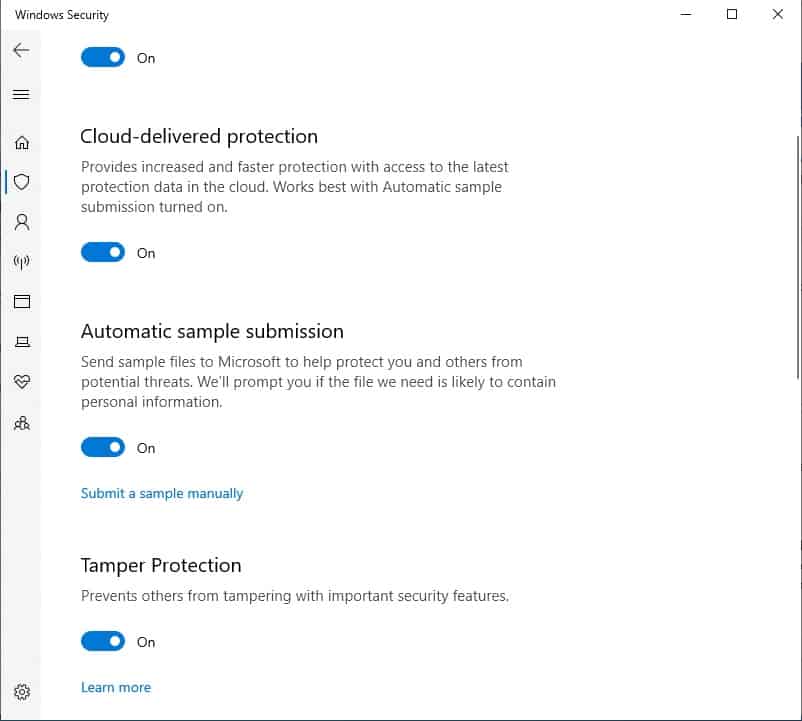
The first one that you could look at is Tamper Protection, which blocks malware from interfering with and altering your device’s antivirus settings. To check that this is turned on:
- Type Windows Security in the Start menu search field.
- Select the Windows Security app from the results.
- Click on Virus & threat protection.
- Look to the bottom of the main panel on this screen and click on Manage settings.
- Tamper Protection is the fourth option on this screen. Make sure it is turned on.
You should also ensure that Real-time protection, Cloud-delivered protection, and Automatic sample submission are turned on.
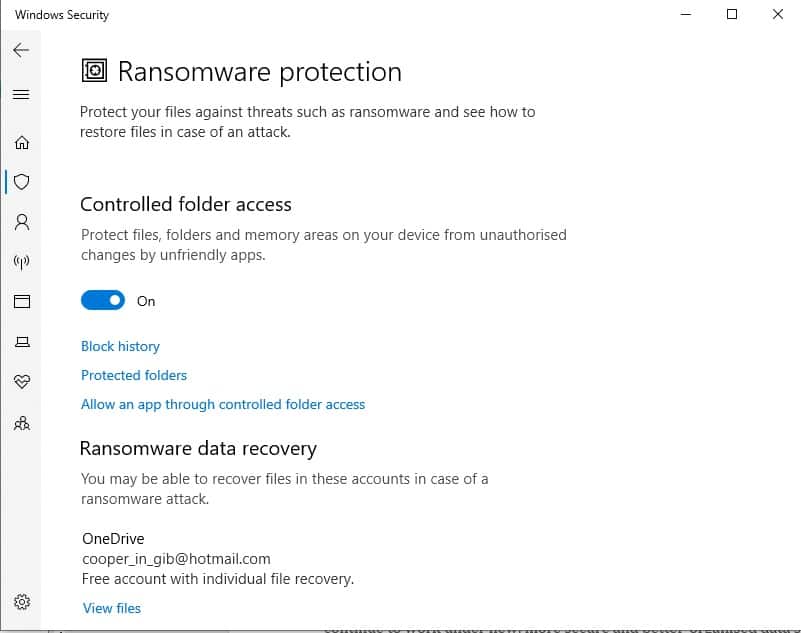
The other major substitute for UAC virtualization protection is the Controlled folder access system. This prevents malware from changing the extensions on files to hide them or altering system folder names. This can also be accessed from the Virus & threat protection settings screen where you turned on Tamper protection.
- In the Virus & threat protection settings screen. Scroll down to Manage controlled folder access and click on it.
- In the next screen, which is Ransomware protection, move the slider for Controlled folder access to On.
- You will be taken to the User Account Control permission popup. Click on Yes to allow the change.
Conclusion
UAC virtualization was a stop-gap measure that enabled the large library of software available for Windows to keep operating. Without this solution, a large amount of the applications available for Windows would have stopped working when Windows Vista was introduced.
With the passage of time, UAC virtualization has become increasingly unnecessary. However, as you have seen, it is still in Windows 10 and you probably will see that it is enabled on your computer.
The virtualization solution for UAC was a clever one and its methods would prove useful to any system protection scenario. In fact, many security systems operate on virtualization, classifying them as “virtual appliances.” The isolation of the operating system and applications works both ways. It can also prevent hackers from getting into the software and tampering with them by blocking off the access route through the operating system.
L’article What is UAC virtualization? est apparu en premier sur Comparitech.
0 Commentaires